Security
Protect your AI-driven enterprise
Red Hat® helps you build a defense-in-depth approach across the infrastructure and application stack, delivering improved security and compliance for hybrid cloud, AI, and digital sovereignty.
Security and digital sovereignty in the age of AI
Today's cybersecurity landscape is evolving rapidly—fragmented perimeters, Al-driven threats, single points of failure, and supply chain vulnerabilities demand multi-layered defenses. Siloed teams, complex data sovereignty requirements, and jurisdictional compliance pressures strain resources, putting your critical data at constant risk.
Open source access without oversight
Teams that use unmanaged open source software and packages leave their organizations vulnerable by inheriting supply chain security issues without the resources to manage them effectively.
Evolving Al-specific threats
Security and compliance requirements shift to accommodate the complexity of external risks, especially as Al continues to scale and develop. Windows of opportunity for exploitation make Al applications and models attractive targets for malicious actors.
Challenges to digital sovereignty
Driven by shifts in geopolitics, supply chains, and Al, digital sovereignty has become critical for organizations and governments needing to maintain technological and economic autonomy.
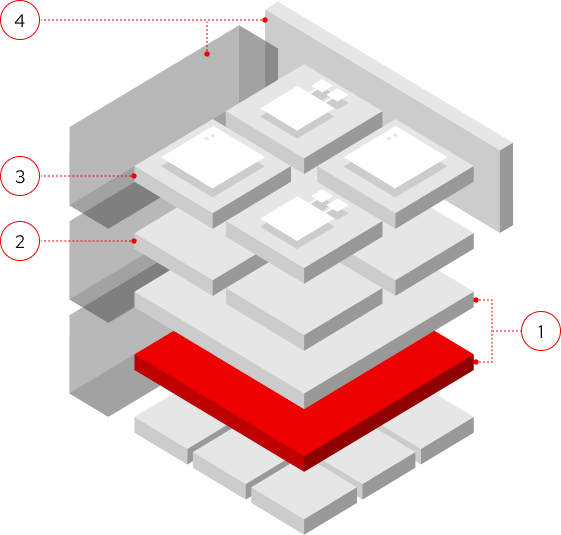
Red Hat Portfolio Security: From the OS to autonomous AI agents
Built around four core areas of Red Hat's layered, defense-in-depth security approach, our technologies help protect your stack, whether you control infrastructure directly or rely on public clouds through our partner ecosystem. By showing enterprises how to implement a layered security approach, your organization remains secure and in control.
Security-focused foundation
Our foundational platforms, Red Hat Enterprise Linux® and Red Hat OpenShift®, are developed using rigorous software supply chain security processes. Each solution provides robust, reliable infrastructure for developing and deploying a wide range of applications, including AI/ML models. Our container security best practices are applied to your entire hybrid cloud environment.
Software and AI supply chain security
Applications and AI systems are treated as containerized software, delivering reliability, governance, and compliance from development to production. Customers can integrate security into their AI workflows with LLM/ML model evaluation and policy enforcement. DevSecOps principles and Red Hat Trusted Software Supply Chain help protect against vulnerabilities, malicious code, and tampering across the entire lifecycle.
Sovereign AI
Red Hat supports organizations in maintaining digital sovereignty by helping keep sensitive data and proprietary models within their own jurisdictional or physical boundaries. Our open hybrid cloud gives customers the building blocks for adaptability, autonomy, and independence.
Security automation at scale
Our integrated approach guides organizations in managing and automating open hybrid cloud environments. We help customers maintain control over their security and compliance by implementing zero trust principles, continuous security updates, and AI-specific guardrails.
- Start with a strong foundation
- Protect the pipeline
- Implement guardrails for AI agents and modals
- Automate security at scale
Integrating security into development, training, and deployment
Red Hat helps secure AI model and application lifecycles through a unified hybrid-cloud platform, like Red Hat OpenShift AI, and runs AI models and apps as containerized software. Paired with DevSecOps tooling like Red Hat Trusted Software Supply Chain, your organization can guard against vulnerabilities, malicious code, and tampering at every stage.
Red Hat technologies for enterprise-level security
Find out how our solutions can support your compliance management goals.
Red Hat AI
Develop AI applications that remain fast and responsive. With layered security and safety, Red Hat AI solutions enable hybrid cloud agility while mitigating risk.
Red Hat Enterprise Linux
Discover the leading enterprise Linux operating system—certified on hundreds of clouds and with thousands of vendors. Our built-in tools ensure compliance and reinforce safety.
Red Hat Ansible Automation Platform
Apply consistent, enterprise-wide automation to streamline and integrate security operations into your processes. Automated access controls, logging, and auditing reduce the risk of misconfigurations and human error.
Red Hat OpenShift
Manage hybrid cloud and multicloud deployments with our enterprise-ready Kubernetes container platform with full-stack automated operations. The platform’s foundational features give you autonomy over policies and controls, increasing container security.
Customer case study
Building unity between developers and operations
Learn more about the DevSecOps approach stc Group took to modernize the application delivery systems using Red Hat OpenShift.
Scaling innovation across industries using open source
Uncover how the Swiss-based IT company delivered safety, reliability, and compliance with its sovereign cloud using Red Hat software solutions.
Find the right partner for you
Red Hat's extensive partner ecosystem has solutions that will align with your security needs, no matter how big or small.
Take the next step
Digital sovereignty readiness
Determine if your organization is well-positioned to manage and scale it's digital autonomy.
How Red Hat is shaping AI, sovereignty, and modernization
Learn how Red Hat is evolving its strategy to meet 3 emerging market trends.
Scaling AI adoption with Red Hat OpenShift AI
Discover how Telenor worked with Red Hat's cloud-native and AI platforms to power its sovereign AI factory.